In 2007, Stina Ehrensvard founded a small startup with a vision: what if you could have a single key to secure all your online accounts against cybercriminals? 12 years later, the internet is still rife with phishing attacks, stolen passwords, hijacked accounts (even among tech-savvy people), and billions of credentials changing hand on dark web markets.
But Ehrensvard has come a long way toward fulfilling her vision. Her company Yubico has manufactured one of the most successful line of hardware authentication keys and has also helped develop open standards for the development of secure authentication technologies. The movement to end password insecurity now counts among its members big names such as Google, Microsoft and Facebook.
In an interview with TechTalks, Ehrensvard discussed authentication, the evolution of Yubico’s security keys and the future of the internet.
What has changed in the past decades?
A few decades ago, in the early years of the internet, every user had very few accounts, each of which could be secured with a simple password. But today, every single one us has dozens of accounts, and tied to those accounts are very sensitive information and functionality. We rely on these accounts for most of our personal and business communications, as well as our banking activities, and inevitably, the control of our home and office appliances.
But while the internet and our digital lives have expanded, one thing that has remained fairly consistent is passwords. Meanwhile, the people who are interested in hacking into our accounts have changed a lot.

“Technically and theoretically, people could hack passwords 20 years ago. But they didn’t do it at scale,” Ehrensvard says. “Today, they have plenty of tools like malware and trojans. It’s not one person hacking. There are armies of hackers collaborating together and using super computers. They’re becoming more sophisticated and advanced.”
Ehrensvard also remarks that as opposed to older ages of financial crime, there’s much less risk associated with cybercrime, which lowers the barrier of entrance for cybercriminals. “Most of the time, cybercriminals don’t get caught,” Ehrensvard says.
With so much value associated with our accounts, and nothing more than a password preventing intruders from accessing them, account hijacking has become a very lucrative business.
In the past years, the authentication space has also gone through some relevant changes. More and more companies have endorsed two-factor authentication (2FA), the practice of requiring users to present more than just passwords to gain access to their accounts.
But adoption of 2FA has been minimal where users have had a choice. According to a 2018 study by Google, less than 10 percent of Gmail users have enabled two-factor authentication on their accounts. Many users find the extra effort required by 2FA applications (such as typing in a one-time password sent to a mobile app) too bothersome and disable them, hoping against hope that their passwords don’t get hacked.
This means for more than 90 percent of users, the only thing standing between them and a malicious hacker is a string of letters, numbers and symbols. As other studies show, an alarming percentage of users neglect password best practices, such as avoiding obvious passwords and avoiding password reuse.
This is where efforts like those of Yubico come in.
How the YubiKey evolved
The idea behind YubiKey, Yubico’s flagship USB security key, was to provide a convenient and reliable way to secure multiple accounts with a single key.
“When I started Yubico, I had the vision for having one key for any number of services, and I want this key to be easy to use for everyone,” Ehrensvard says. “Instead of using the one-time password (OTP), we suggested using public key cryptography.”
Public key cryptography, also known as asymmetric cryptography, is a form of encryption that uses a key-pair to protect information. Every key-pair is composed of a public and a private key. The public key is usually used for identification and sending encrypted information. Private keys are used to sign sensitive data and to decrypt information encrypted with the public key.
Every YubiKey has a public key, which can be registered with a user account. The corresponding private key remains exclusively on the YubiKey device. When users register their YubiKey with their account (say Gmail or Facebook), the device’s public key is registered with their account. Afterwards, when they want to log in to their accounts with a new device, the users plug in their YubiKey to their computer, which uses the private key to verify their identity with the corresponding public key. The YubiKey proved to be a secure and convenient alternative to OTP and SMS two-factor authentication.
One of the great benefits of YubiKey is that a single key can be registered with any number of accounts. Also, if hackers breach the servers of a service provider, they will only be able to obtain the public keys of users, which will be of no use without their corresponding private keys.
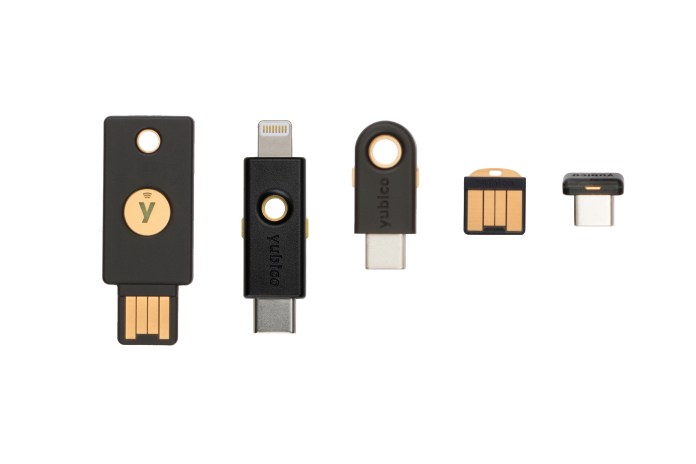
Since Yubico introduced the first YubiKey, the device has gone through several revolutions and releases. Yubico released various versions of the device, including an NFC-enabled version that provided 2FA for mobile devices. More recently, Yubico released YubiKey 5Ci, a security key with a Lightning and USB-C connectors to use with iPhones and iPads.
One of the key successes of YubiKey was the consistent user experience it has provided. “The device has gone through an evolution, but the user interface and experience has remained the same,” Ehrensvard says.
Most YubiKeys are simple devices with a button that generates a cryptographic string every time it is touched. This little detail, called “touch to sign,” has been one of the key innovations behind YubiKey, and has been consistent across all generations of Yubico’s products. Though simple on the surface, touch to sign solves a very important problem.
“Touch to sign makes sure that a real user is sitting behind the computer and is signing on with the key. It can’t be a remote hacker,” Ehrensvard says.
Yubico’s role in shaping passwordless authentication

Aside from its line of security keys, Yubico has also played an important role in the evolution of authentication.
In 2012, Yubico partnered with Google to protect its users from phishing attacks and other cyberthreats. Google integrated support for YubiKey in its services, giving its users a very strong alternative to OTPs and SMS codes. SMS codes have long been proven to be insecure. Time-based authenticator apps are also prone to compromises.
In contrast, YubiKey is extremely resilient to phishing and other cyberattacks. “Even with basic setups where YubiKeys aren’t used in every login, we haven’t seen any phishing attacks on YubiKey-protected accounts,” Ehrensvard says.
In the years that followed, other major companies, including Dropbox, Facebook and Microsoft also added support for YubiKey.
Yubico also became an important member of FIDO, an alliance of organizations that aims to promote secure and passwordless authentication. Yuico’s technologies and experience became pivotal to the standards designated by FIDO, including the important U2F hardware key specification.
In 2019, FIDO and W3C jointly introduce WebAuthn, a standard that allows all major browsers to support passwordless authentication through hardware keys or secure authenticator apps. WebAuthn paved the way for mass adoption of passwordless authentication across a wide range of online services and applications.
“Finally, we’re seeing the web has a new authentication standard and all the leading platforms are supporting it. Finally, we have a solution that can prevent phishing at scale,” Ehrensvard says. “We’re happy to be part of that movement.”
The future of authentication
As secure and passwordless authentication picks up steam, more and more companies are joining the movement. “Anyone can implement support for WebAuthn in days. And it’s supported by all major browsers,” Ehrensvard says.
Also important is the growing trend of devices with built-in support for FIDO authentication standards. Last year, Google released a Chromebook with a built-in U2F authenticator, and there are now several lines of Android phone that have native U2F features.
“I’m a big believer in the built-in authenticator because that’s where it scales to the mass market. We want WebAuthn to happen and everyone to start using it,” Ehrensvard says.
How will this affect hardware security vendors such as Yubico? “YubiKey will be a backup if you lose your phone, and it will still be a more convenient option for high-security applications,” Ehrensvard explains. “An external authenticator that’s not tied to your computer, that’s not connected to the internet and only does one thing will always be a better security solution.”
Can we be hopeful for a hack-less future? “The internet is never going to be a safe place,” Ehrensvard reminds. “But it will be better, it will be safer, people will be more educated. I think there’s hope for a next generation, safer internet, where we can do things that we really can’t do today, like voting, dealing with the security challenges of cryptocurrencies, and IoT security challenges.”




















